GitHub with SSH keys
November 29th, 2020The authentication on GitHub using automatically generated tokens and saved in Windows Credential Manager works like a charm. For as long as you need to access only one GitHub account. For the time being the workaround for another account is to authenticate with an ssh key.
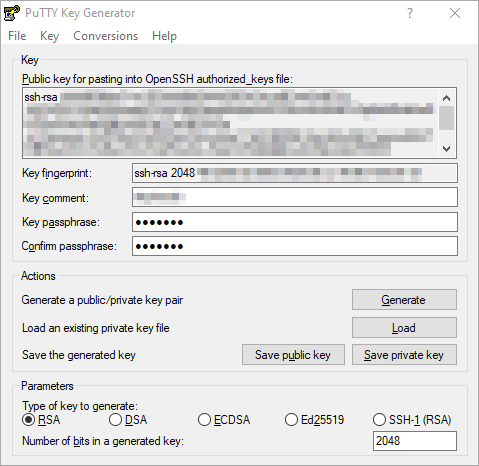
Using OpenSSH in the first step could have saved me a lot of time, but I made a bigger loop via PuTTYen. Generated an RSA 2048 bit key and exported to all formats supported by the tool:
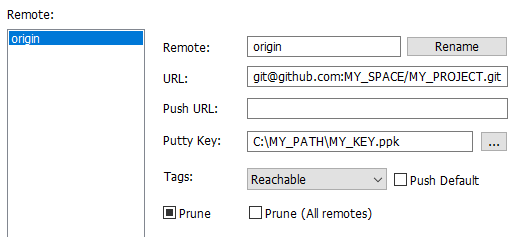
Unfortunately, the simplest approach via TortoiseGit did not work:
Ending with the response:
> git push -u origin main
git@github.com: Permission denied (publickey).
fatal: Could not read from remote repository.
Please make sure you have the correct access rights
and the repository exists.
It turned out, git did not look for the configured key at all. The following helped:
- Store the private key under %HOMEPATH%.ssh\id_rsa (~/.ssh/id_rsa) in the OpenSSH format (—–BEGIN RSA PRIVATE KEY—– and so on)
- Store the public key under %HOMEPATH%.ssh\id_rsa.pub (~/.ssh/id_rsa.pub) in the OpenSSH format (ssh-rsa XXXX…== COMMENT)
A few good-to-know things:
- Export the public key out of the OpenSSH private+public container to RFC4716 format:
ssh-keygen -e -f ~/.ssh/id_rsa > PATH_TO_RFC4716_PUBLIC_KEY
-
Export RFC4716 public key to OpenSSH format:
ssh-keygen -i -f PATH_TO_RFC4716_PUBLIC_KEY > ~/.ssh/id_rsa.pub
-
GitHub awaits the username “git” for the SSH protocol, not the one of your account.
- The correct URL schemes for the SSH protocol:
- ssh://git@github.com/x/y.git
- git@github.com:x/y.git
- TortoiseGit (or rather the manager helper) is storing credentials (tokens) in Windows Credential Manager under “Windows Credentials”, named e.g. https://github.com/